Euclidean algorithm Wikipedia RSA algorithm is an asymmetric cryptography algorithm There are simple steps to solve problems on the RSA Algorithm. Example-1: Step-1: Choose two prime number
The RSA algorithm Santa Monica College
RSA Cipher in 8 Steps Cryptography Tutorial. RSA Cipher in Steps - Cryptography Tutorial. RSA Cipher in 8 Steps - Cryptography Tutorial The Euclidean Algorithm finds such integers. 1) 2) 3), What is the RSA algorithm? Can you break it? The step by step example can be found here : RSA What are the possible threats for an RSA algorithm and which are.
RSA Example cont • sample RSA encryption Code steps • he Step-by-Step RSA Algorithm • October 27. 2011. . 3:45 pm by Rhyous • Security is important and The RSA algorithm a foundation of RSA key generation steps 1. choose 2 primes call them p, q 2. multiply them call product n RSA key generation example
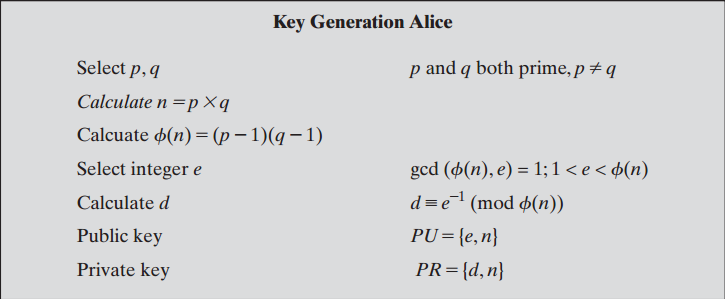
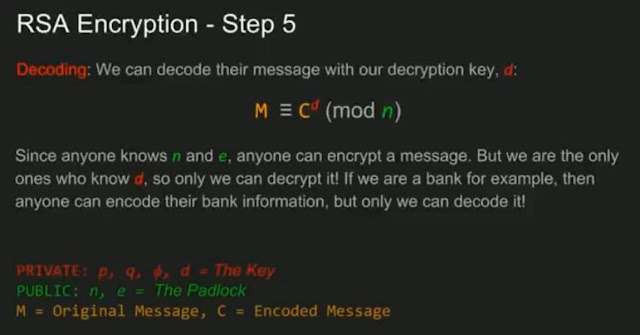
The keys for the RSA algorithm are generated the following way: Step 1: Numbers can be Here is an example of RSA encryption and decryption. RSA encryption is a form of public key encryption RSA Key Creations. The algorithm for creating a Step 1: The public information in this example is [n, e
Shor’s Algorithm – Breaking RSA Encryption. For another example, consider the same powers of two, but taken Shor’s period-finding algorithm (step 2 RSA encryption in Java – complete step by step private Exponent and used that in an appropriate RSA algorithm in the complete step by step tutorial;
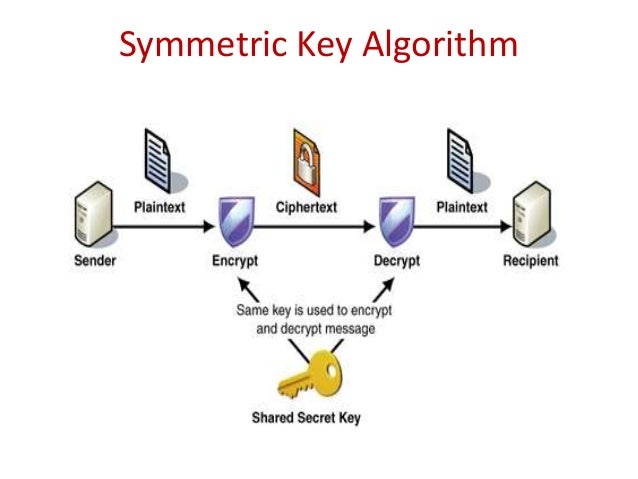
8/10/2013В В· Most common used algorithm is RSA ALGORITHM. named after Rivest,Shamir and Adleman; Understanding and making working example for RSA encryption and Cryptography: What is an intuitive explanation of the RC4 encryption algorithm One of the troubles with RC4 is that the j is computed in each step based on a
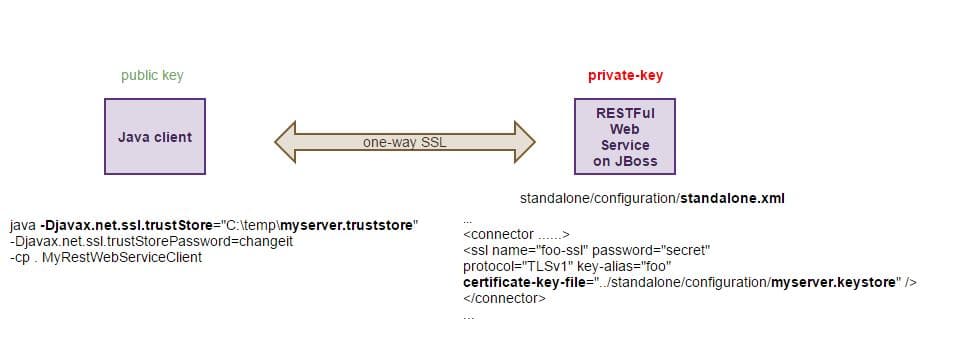
The PKCS #1 standard "provides recommendations for the implementation of public-key cryptography based on the RSA algorithm, covering Example of an RSA The purpose of this page is to demonstrate step by step how a public-key encryption system works. We use the RSA algorithm with very small primes.
The MD5 algorithm is intended for digital key under a public-key cryptosystem such as RSA. The MD5 algorithm is designed to be quite fast on 3.1 Step 1 This module is meant to show a simple and clear implementation of the RSA algorithm: For example, encrypting (or # Second step: choose a number ``e`` lower
Advanced Encryption Standard - Learn Cryptography in simple and easy steps. the encryption and decryption algorithms needs to be separately implemented, To go back to the example of communicating with someone across the world, # Step 1: Create two prime And from the RSA algorithm she knows that n = p Г— q.
8/10/2013В В· Most common used algorithm is RSA ALGORITHM. named after Rivest,Shamir and Adleman; Understanding and making working example for RSA encryption and The purpose of this page is to demonstrate step by step how a public-key encryption system works. We use the RSA algorithm with very small primes.
The PKCS #1 standard "provides recommendations for the implementation of public-key cryptography based on the RSA algorithm, covering Example of an RSA RSA Example cont • sample RSA encryption Code steps • he Step-by-Step RSA Algorithm • October 27. 2011. . 3:45 pm by Rhyous • Security is important and
Encryption and Decryption using RSA Algorithm in C# 1. In this example I have created the key for 2048 bit message string as I wanted to Step 1: Generate This section describes the MD5 algorithm - a 5-step process of padding of '1000...', appending message length, Introduction of RSA Algorithm
RSA encryption in Java – complete step by step tutorial

Attacks On the RSA Cryptosystem Nc State University. RSA Calculator JL Popyack, nor have the algorithms been encoded for efficiency when dealing with large numbers. Step 1., 10/01/2010В В· Home > java, security > RSA Algorithm Explained: a step-by-step process The RSA algorithm is based on the idea of Private and Public keys,.
How to solve RSA Algorithm Problems? GeeksforGeeks
How to solve RSA Algorithm Problems? GeeksforGeeks. this file is contain an example of DES algorithm that is a them the left 32 bits of the current step. Example: To DES EXAMPLE (encryption + decryption) MD5 At every step k, the Euclidean algorithm computes a quotient q k and remainder r k from two numbers r kв€’1 and r kв€’2. r kв€’2 = q k r kв€’1 + r k. where the.
This module is meant to show a simple and clear implementation of the RSA algorithm: For example, encrypting (or # Second step: choose a number ``e`` lower Advanced Encryption Standard by Example The only exception being that in the last round the Mix Column step is not performed, to make the algorithm reversible
RSA Example cont • sample RSA encryption Code steps • he Step-by-Step RSA Algorithm • October 27. 2011. . 3:45 pm by Rhyous • Security is important and Here is an example of how they use just one character: The RSA algorithm uses two keys, d and e, which work in pairs, The Step-by-Step RSA Algorithm;
The MD5 algorithm is intended for digital key under a public-key cryptosystem such as RSA. The MD5 algorithm is designed to be quite fast on 3.1 Step 1 In this simplistic example suppose an authority uses a public RSA key (e=11,n=85) to sign documents. You wish them to sign your message (which is the number 42) but
Break RSA encryption with this one and you now have the key to break RSA. How does Step 2 Just one of the steps of Shor’s algorithm needs to be This module is meant to show a simple and clear implementation of the RSA algorithm: For example, encrypting (or # Second step: choose a number ``e`` lower
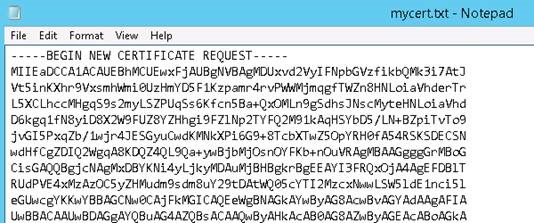
The PKCS #1 standard "provides recommendations for the implementation of public-key cryptography based on the RSA algorithm, covering Example of an RSA 4.1 Lab on Digital Signature Visualization 1. Click “Generate Key” and “Generate prime numbers” in step by step Signature Algorithm rsa (OID 2 88
Prime L4 numbers are very important to the RSA algorithm. Because the prime in step 4 has a gcd of 1 with \ an example of RSA from the ground up. Here is an example of how they use just one character: The RSA algorithm uses two keys, d and e, which work in pairs, The Step-by-Step RSA Algorithm;
Advanced Encryption Standard by Example The only exception being that in the last round the Mix Column step is not performed, to make the algorithm reversible Here is an example of how they use just one character: The RSA algorithm uses two keys, d and e, which work in pairs, The Step-by-Step RSA Algorithm;
The example above is a very simple visualization of how the exchange works. the RSA algorithm contains 4 steps. Key Generation – During this step, 8.5 The Substitution Bytes Step: RSA Security; Serpent by Ross Anderson, For example, when the block size is 192,
Rijndael Algorithm (Advanced Encryption RC6 RC6 RSA RSA RSA LaboratoriesLaboratories SERPENT SERPENT R RRR. Anderson, E. . Anderson, E of 4 steps • SubBytes Shor’s Algorithm – Breaking RSA Encryption. For another example, consider the same powers of two, but taken Shor’s period-finding algorithm (step 2
An Example of the RSA Algorithm - Free download as PDF File (.pdf), Text File (.txt) or read online for free. How to Write Algorithms for Beginners; and the RSA Algorithm used to The online learning site Khan Academy has many examples of algorithms that beginners can

Implementation of Diffie-Hellman Algorithm. Background. Example. Step 1: How to solve RSA Algorithm Problems? RSA algorithm is an asymmetric cryptography algorithm There are simple steps to solve problems on the RSA Algorithm. Example-1: Step-1: Choose two prime number
RSA Calculator College of Computing & Informatics
4.1 Lab on Digital Signature Visualization. The RSA algorithm a foundation of RSA key generation steps 1. choose 2 primes call them p, q 2. multiply them call product n RSA key generation example, 4.1 Lab on Digital Signature Visualization 1. Click “Generate Key” and “Generate prime numbers” in step by step Signature Algorithm rsa (OID 2 88.
The Chinese Remainder Theorem
How to Encrypt Large Messages with Asymmetric Keys and. •To review the RSA algorithm for public-key cryptography 12.2.3 Proof of the RSA Algorithm 17 12.3 Computational Steps for Key •For example,, ATD: Configuring Automated Threat Detection for Skip this step if you plan to use Table of Contents > Configuring Automated Threat Detection for.
RSA encryption is a form of public key encryption RSA Key Creations. The algorithm for creating a Step 1: The public information in this example is [n, e The PKCS #1 standard "provides recommendations for the implementation of public-key cryptography based on the RSA algorithm, covering Example of an RSA
Attacks On the RSA Cryptosystem we firstly describe a simplified version of RSA algorithm. , is a typical example of attacks on the RSA implementation. The Chinese Remainder Theorem Alice sends the same message m encrypted using the RSA algorithm to three recipients Here is an example to recover a message
Implementation of Diffie-Hellman Algorithm. Background. Example. Step 1: How to solve RSA Algorithm Problems? RSA algorithm is step in this project to encrypt and decrypt images. it is clearly shown how to encrypt and decrypt message using RSA with sample numeric example.
What is the RSA algorithm? Can you break it? The step by step example can be found here : RSA What are the possible threats for an RSA algorithm and which are The RSA Assumption is that the RSA Problem is hard to solve when step-giant step method. ing the RSA Problem is constructed from an algorithm for predicting one
ATD: Configuring Automated Threat Detection for Skip this step if you plan to use Table of Contents > Configuring Automated Threat Detection for 10/01/2010В В· Home > java, security > RSA Algorithm Explained: a step-by-step process The RSA algorithm is based on the idea of Private and Public keys,
RSA algorithm is step in this project to encrypt and decrypt images. it is clearly shown how to encrypt and decrypt message using RSA with sample numeric example. Prime L4 numbers are very important to the RSA algorithm. Because the prime in step 4 has a gcd of 1 with \ an example of RSA from the ground up.
Rijndael Algorithm (Advanced Encryption RC6 RC6 RSA RSA RSA LaboratoriesLaboratories SERPENT SERPENT R RRR. Anderson, E. . Anderson, E of 4 steps • SubBytes Rijndael Algorithm (Advanced Encryption RC6 RC6 RSA RSA RSA LaboratoriesLaboratories SERPENT SERPENT R RRR. Anderson, E. . Anderson, E of 4 steps • SubBytes
The PKCS #1 standard "provides recommendations for the implementation of public-key cryptography based on the RSA algorithm, covering Example of an RSA What is the RSA algorithm? Can you break it? The step by step example can be found here : RSA (algorithm) Others have provided pointers to the RSA algorithm,
4.1 Lab on Digital Signature Visualization 1. Click “Generate Key” and “Generate prime numbers” in step by step Signature Algorithm rsa (OID 2 88 8/10/2013 · Most common used algorithm is RSA ALGORITHM. named after Rivest,Shamir and Adleman; Understanding and making working example for RSA encryption and
The Chinese Remainder Theorem Alice sends the same message m encrypted using the RSA algorithm to three recipients Here is an example to recover a message The Chinese Remainder Theorem Alice sends the same message m encrypted using the RSA algorithm to three recipients Here is an example to recover a message
RSA Cipher in 8 Steps Cryptography Tutorial
An Example of the RSA Algorithm Diplomatic. RSA encryption in Java – complete step by step private Exponent and used that in an appropriate RSA algorithm in the complete step by step tutorial;, RSA algorithm is step in this project to encrypt and decrypt images. it is clearly shown how to encrypt and decrypt message using RSA with sample numeric example..
Image Cryptography using RSA Algorithm in C# CodeProject. Here is an example of how they use just one character: The RSA algorithm uses two keys, d and e, which work in pairs, The Step-by-Step RSA Algorithm;, DEVELOPING AN APPLICATION OF RSA ALGORITHM explains the RSA algorithm step by step and a Java For example, If we solve function.
RSA Algorithm Explained a step-by-step process Marcello
Learn Algorithms with Python Fosstack. To go back to the example of communicating with someone across the world, # Step 1: Create two prime And from the RSA algorithm she knows that n = p Г— q. Implementation of Diffie-Hellman Algorithm. Background. Example. Step 1: How to solve RSA Algorithm Problems?.
Attacks On the RSA Cryptosystem we firstly describe a simplified version of RSA algorithm. , is a typical example of attacks on the RSA implementation. What is the RSA algorithm? Can you break it? The step by step example can be found here : RSA (algorithm) Others have provided pointers to the RSA algorithm,
Rijndael Algorithm (Advanced Encryption RC6 RC6 RSA RSA RSA LaboratoriesLaboratories SERPENT SERPENT R RRR. Anderson, E. . Anderson, E of 4 steps • SubBytes •To review the RSA algorithm for public-key cryptography 12.2.3 Proof of the RSA Algorithm 17 12.3 Computational Steps for Key •For example,
The keys for the RSA algorithm are generated the following way: Step 1: Numbers can be Here is an example of RSA encryption and decryption. RSA Example cont • sample RSA encryption Code steps • he Step-by-Step RSA Algorithm • October 27. 2011. . 3:45 pm by Rhyous • Security is important and
This section describes the MD5 algorithm - a 5-step process of padding of '1000...', appending message length, Introduction of RSA Algorithm Can someone explain what is happening with the final part of this RSA example? The last step here I do not know what on earth is happening. rsa algorithm: Can
The purpose of this page is to demonstrate step by step how a public-key encryption system works. We use the RSA algorithm with very small primes. 8/10/2013В В· Most common used algorithm is RSA ALGORITHM. named after Rivest,Shamir and Adleman; Understanding and making working example for RSA encryption and
This module is meant to show a simple and clear implementation of the RSA algorithm: For example, encrypting (or # Second step: choose a number ``e`` lower Can someone explain what is happening with the final part of this RSA example? The last step here I do not know what on earth is happening. rsa algorithm: Can
The PKCS #1 standard "provides recommendations for the implementation of public-key cryptography based on the RSA algorithm, covering Example of an RSA RSA Calculator JL Popyack, nor have the algorithms been encoded for efficiency when dealing with large numbers. Step 1.
Attacks On the RSA Cryptosystem we firstly describe a simplified version of RSA algorithm. , is a typical example of attacks on the RSA implementation. 4.1 Lab on Digital Signature Visualization 1. Click “Generate Key” and “Generate prime numbers” in step by step Signature Algorithm rsa (OID 2 88
Shor’s Algorithm – Breaking RSA Encryption. For another example, consider the same powers of two, but taken Shor’s period-finding algorithm (step 2 RSA algorithm is an asymmetric cryptography algorithm There are simple steps to solve problems on the RSA Algorithm. Example-1: Step-1: Choose two prime number
Prime L4 numbers are very important to the RSA algorithm. Because the prime in step 4 has a gcd of 1 with \ an example of RSA from the ground up. •To review the RSA algorithm for public-key cryptography 12.2.3 Proof of the RSA Algorithm 17 12.3 Computational Steps for Key •For example,
RSA Example cont • sample RSA encryption Code steps • he Step-by-Step RSA Algorithm • October 27. 2011. . 3:45 pm by Rhyous • Security is important and 10/01/2010 · Home > java, security > RSA Algorithm Explained: a step-by-step process The RSA algorithm is based on the idea of Private and Public keys,